The capolicy.inf contains basic settings that can or should be specified before installing a certificate authority. In simple terms, it can be said that no certificate authority should be installed without it.
Create a capolicy.inf
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
The file is not created automatically. Accordingly, it must be created before installing a certificate authority and, in case of migration or Recovery be transferred from the source system.
Version
Each capolicy.inf must start with the "version" extension with the following content.
[Version] Signature= "$Windows NT$"
Strings
In the "Strings" section text variables can be defined, e.g. to convert object identifiers into an easily readable format.
[Strings] szOID_NAME_CONSTRAINTS = "2.5.29.30"
Extensions
The "Extensions" section allows to define or modify extensions in the certificate request (and thus in the resulting certificate).
Example: Setting the "Name Constraints" extension of an issuing certification authority to allow DNS names in the Subject Alternative Name for "adcslabor.de" and to prevent the use of the Common Name.
[Extensions]
Critical = %szOID_NAME_CONSTRAINTS%
%szOID_NAME_CONSTRAINTS% = "{text}"
continue = "SubTree=Include&"
continue = "DNS = adcslabor.de&"
continue = "SubTree=Exclude&"
continue = "DIRECTORYNAME = CN=&"
[Strings]
szOID_NAME_CONSTRAINTS = "2.5.29.30"
According to RFC 5280, name constraints are ignored for certificates for root certificate authorities.
Example: Modify the "Key Usage" extension of a root certification authority. Remove "Digital Signature" and set the "Key Usage" extension as critical.
[Extensions] 2.5.29.15 = AwIBBg== Critical = 2.5.29.15
Example: Removing the extensions "CA Version" and "Previous CA Certificate Hash" from a root certification authority certificate.
[Extensions] 1.3.6.1.4.1.311.21.1= ; szOID_CERTSRV_CA_VERSION 1.3.6.1.4.1.311.21.2= ; szOID_CERTSRV_PREVIOUS_CERT_HASH
See also the following articles:
BasicConstraintsExtension
The BasicConstraintsExtension section allows to define the path length constraint of a certification authority certificate. This setting should not be applied to certificates of a root certification authority to maintain flexibility. Instead, the extension should be configured for certificates of issuing certification authorities.
[BasicConstraintsExtension] PathLength=0 Critical=TRUE
Conforming CAs MUST include this extension in all CA certificates that contain public keys used to validate digital signatures on certificates and MUST mark the extension as critical in such certificates.
https://tools.ietf.org/html/rfc5280#section-4.2.1.9
See also article "Basics: Path Length Constraint„.
PolicyStatementExtension
[PolicyStatementExtension] Policies=InternalPolicy [InternalPolicy] OID=1.3.6.1.4.1.99999.300.2.1.4.3.1 Notice=CPS is to be found at: http://pki.adcslabor.de/CPS/index.html URL=http://pki.adcslabor.de/CPS/index.html
The Trusted Platform Module (TPM) Key Attestation can optionally be used with issuance guidelines. If it is planned to use this, it makes sense to include the issuance guidelines defined for this purpose in the Certification Authority certificate.
See also article "Configuring the Trusted Platform Module (TPM) Key Attestation„.
Alternatively, you can also include the AnyPolicy object identifier:
[PolicyStatementExtension] Policies=AllIssuancePolicy [AllIssuancePolicy] OID=2.5.29.32.0
This procedure should be avoided, is according to RFC 5280 but explicitly allowed.
When a CA does not wish to limit the set of policies for certification paths that include this certificate, it MAY assert the special policy anyPolicy, with a value of { 2 5 29 32 0 }.
https://tools.ietf.org/html/rfc5280#section-4.2.1.14
Here is a list of common (general) exhibition guidelines.
| OID | Description |
|---|---|
| 2.5.29.32.0 | All Issuance Policies (AnyPolicy) |
| 1.3.6.1.4.1.311.21.32 | TPM Key AttestationUser Credentials: (Low Assurance) |
| 1.3.6.1.4.1.311.21.31 | TPM Key AttestationEndorsement Certificate: (Medium Assurance) |
| 1.3.6.1.4.1.311.21.30 | TPM Key AttestationEndorsement Key: (High Assurance) |
EnhancedKeyUsageExtension
In the "EnhancedKeyUsageExtension" section, the "Extended Key Usage" extension of a certificate authority certificate can be edited in order to limit the range for issuing certificates.
Microsoft uses the term "Enhanced Key Usage", the correct name according to RFC 5280 is "Extended Key Usage"..
[EnhancedKeyUsageExtension] OID=1.3.6.1.5.5.7.3.1 ; Client Authentication OID=1.3.6.1.5.5.7.3.2 ; Server Authentication OID=1.3.6.1.5.5.7.3.9 ; OCSP Signing OID=1.3.6.1.4.1.311.21.5 ; Private Key Archival Critical=FALSE
Concerning restrictions of extended key usages in certification authority certificates, the RFC 5280 Unfortunately, this is not the case. The evaluation must therefore be carried out individually for each application.
The CA/Browser Forum (CAB) responsible for certificate processing in popular browsers. recommends For example, for SSL, it restricts the extended key usages of a certification authority and recommends marking the extension as non-critical.
Regarding smart card registration domain controllers ignore the restriction of extended key usages but in the default setting, for example, completely.
See also the following articles:
- Basics: Restricting Extended Key Usage (EKU) in Certification Authority Certificates
- Domain controller does not check extended key usage on smart card login
In addition to the provided Extended Key Usages, restrictions should always include "Private Key Archival" and "OCSP Signing". If a network device enrollment service (NDES) is connected to the certification authority, the "Certificate Request Agent" Extended Key Usage is also required.
Here is a list of common extended key usages:
| OID | Description |
|---|---|
| 1.3.6.1.4.1.311.20.2.1 | Certificate Request Agent |
| 1.3.6.1.5.5.7.3.2 | Client Authentication |
| 1.3.6.1.5.5.7.3.3 | Code Signing |
| 1.3.6.1.4.1.311.10.3.13 | Lifetime Signing |
| 1.3.6.1.4.1.311.10.3.12 | Document Signing |
| 1.3.6.1.4.1.311.80.1 | Document Encryption |
| 1.3.6.1.4.1.311.10.3.4 | Encrypting file system |
| 1.3.6.1.4.1.311.10.3.4.1 | File Recovery |
| 1.3.6.1.5.5.7.3.5 | IP Security End System |
| 1.3.6.1.5.5.8.2.2 | IP Security IKE Intermediate |
| 1.3.6.1.5.5.7.3.6 | IP Security Tunnel Endpoint |
| 1.3.6.1.5.5.7.3.7 | IP Security User |
| 1.3.6.1.4.1.311.21.6 | Key Recovery Agent |
| 1.3.6.1.4.1.311.10.3.11 | Key Recovery |
| 1.3.6.1.5.2.3.5 | KDC Authentication |
| 1.3.6.1.4.1.311.10.3.1 | Microsoft Trust List Signing |
| 1.3.6.1.4.1.311.10.3.10 | Qualified Subordination |
| 1.3.6.1.4.1.311.10.3.9 | Root List Signer |
| 1.3.6.1.5.5.7.3.4 | Secure E-mail |
| 1.3.6.1.5.5.7.3.1 | Server Authentication |
| 1.3.6.1.4.1.311.20.2.2 | Smartcard Logon |
| 1.3.6.1.5.5.7.3.8 | Time Stamping according to RFC 3161 |
| 1.3.6.1.5.5.7.3.9 | OCSP Signing |
| 1.3.6.1.4.1.311.54.1.2 | Remote Desktop Authentication |
| 1.3.6.1.4.1.311.21.5 | Private Key Archival |
NameConstraintsExtension
Allows the definition of name restrictions for the certification authority certificate.
[NameConstraintsExtension] Include = PermittedSubtrees Critical = True [PermittedSubtrees] DirectoryName = CN=ADCS Labor Test Issuing CA 1-Xchg DNS = .intra.adcslabor.de
See article "Basics: Name Constraints„.
Certsrv_Server
In this section, settings for the certification authority process can be defined.
| Parameter | Description |
|---|---|
| RenewalKeyLength | Applied only when renewing the certificate authority certificate with a new key pair. Indicates the key size to be used in this case. |
| RenewalValidityPeriod | Affects only root Certification Authorities. Used only when renewing the certification authority certificate of a root certification authority (this authority itself determines its own certificate validity). |
| RenewalValidityPeriodUnits | Affects only root Certification Authorities. Used only when renewing the certification authority certificate of a root certification authority (this authority itself determines its own certificate validity). |
| AlternatesignatureAlgorithm | Affects only root Certification Authorities. If the value is set to "0", the PKCS#1 padding scheme version 1.5 is used. If the value is set to "1", the PKCS#1 padding scheme version 2.1 is used. |
| ForceUTF8 | Affects only root Certification Authorities. Forces the encoding of the certificate authority's "Common Name" in UTF-8 (Otherwise only if it contains special characters). May cause compatibility problems and should therefore not be used if possible. |
| LoadDefaultTemplates | Affects only Active Directory-integrated certificate authorities (Enterprise CA). If the value is set to "1" or not defined, a set of default certificate templates is automatically published on the certification authority - therefore the value should be defined and set to "0" to prevent this. |
See also the following articles:
- Deploy PKCS#1 version 2.1 for a root CA (owned and issued certificates)
- Description of the necessary configuration settings for the "Common PKI" certificate profile
- (Re-)Installing the Microsoft Standard Certificate Templates
Example of typical settings for a root certification authority:
[Certsrv_Server] RenewalKeyLength=4096 RenewalValidityPeriod=Years RenewalValidityPeriodUnits=8 AlternateSignatureAlgorithm=0 ForceUTF8=1
Example of typical settings of an issuing certification authority:
[Certsrv_Server] RenewalKeyLength=4096 LoadDefaultTemplates=0 AlternateSignatureAlgorithm=0
In the last "official" book on Microsoft Active Directory Certificate Services, "Microsoft Windows Server 2008 PKI and Certificate Security" by Brian Komar incorrectly refers to DiscreteSignatureAlgorithm, and the values were exactly reversed. At the time the book went to press, this was also correct, but with the transition from the beta version of Windows Server 2008 to the final version, the directive was renamed to "AlternateSignatureAlgorithm", including the reverse functionality. Thus, PKCS#1 was still used as the default in version 1.5 if the directive was not explicitly configured.
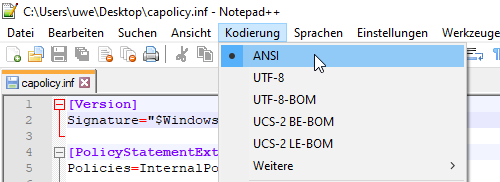
Save the file
The file must be saved in the C:\Windows directory with ANSI encoding before configuring the certificate authority role.
The designation "ANSI" corresponds to the character code Windows-1252 (Latin-1, Western European) in the Windows ecosystem.
Legacy and unusual settings
For the sake of completeness, here are some settings that are no longer relevant in practice.
CRLDistributionPoint and AuthorityInformationAccess
In this section, an extension for revocation list distribution points or for access to job information in the certificate request can be entered.
The section should no longer be used. Sections in capolicy.inf (with the exception of the CertSrv_Server section) are written to the certificate request for the certification authority and are overwritten by the parent certification authority anyway. So the paths are set in the configuration of the parent certificate authority. If you want to customize the revocation list distribution points or for access to job information for the certification authority, you do this via the registration of the installed certification authority.
[CRLDistributionPoint] URL=http://pki.adcslabor.de/CertData/MeineCrl.crl [AuthorityInformationAccess] URL=http://pki.adcslabor.de/CertData/MeinCaZertifikat.crt
Also, the "Empty=true" directive in these sections is no longer required for root CA certificates since Windows Server 2008 and newer.
See also article "Token for CDP and AIA configuration of a certification authority„.
Settings that can also be set via the registration of the certification authority
The following settings can be set in the CertSrv_Server section. They are optional and identical to the value of the same name in the certification authority registration. Thus, it makes sense to set them there as well after a certification authority installation.
The "Unit" values are given in the following format: "Minutes", "Hours", "Days", "Weeks", "Months", "Years".
| Parameter | Description |
|---|---|
| ClockSkewMinutes | Describes the difference (plus/minus) of issued certificates to the system time in minutes to compensate for any time differences. |
| CRLPeriod | Describes the units for the validity of the blacklists. |
| CRLPeriodUnits | Describes the numerical value for the associated unit. |
| CRLOverlapPeriod | Describes the units for the overlap period of the revocation lists. |
| CRLOverlapUnits | Describes the numerical value for the associated unit. |
| CRLDeltaPeriodUnits | Describes the units for the validity of the delta revocation lists. |
| CRLDeltaPeriod | Describes the numerical value for the associated unit. |
| CRLDeltaOverlapUnits | Describes the units for the overlap period of the delta revocation lists. |
| CRLDeltaOverlapPeriod | Describes the numerical value for the associated unit. |
Unusual other settings
| Parameter | Description |
|---|---|
| EnableKeyCounting | If this option is enabled (value set to "1"), a counter is incremented each time the private key is used. However, this function must be supported by the corresponding key storage provider. |
Related links:
- Umlauts in certification authority certificates
- Basics: Restricting Extended Key Usage (EKU) in Certification Authority Certificates
- Frequently Used Extended Key Usages and Issuance Policies
- Basics: key algorithms, signature algorithms and signature hash algorithms
- Deploy PKCS#1 version 2.1 for a root CA (owned and issued certificates)
- Description of the necessary configuration settings for the "Common PKI" certificate profile
- Use name constraints to allow a certification authority to issue certificates only for specific domain names
- (Re-)Installing the Microsoft Standard Certificate Templates
- Token for CDP and AIA configuration of a certification authority
- Character encoding in the Subject Distinguished Name of certificate requests and issued certificates
External sources
- Prepare the CAPolicy.inf File (Microsoft)
- Windows Server 2008 R2 CAPolicy.inf Syntax (Microsoft, archive link)
- Baseline Requirements for the Issuance and Management of Publicly-Trusted Certificates (CA/Browser Forum)
- Three decades of Unicode (Golem Media GmbH)
Comments are closed.