The following is an overview of the events generated by the online responder (OCSP) in the Windows Event Viewer.
The events of the online responder are not officially documented. The following list was generated using the Windows Event Log Messages (WELM) tool.
The Online Responder (Online Certificate Status Protocol, OCSP) is an alternative way of providing revocation status information for certificates. Entities that want to check the revocation status of a certificate do not have to download the complete list of all revoked certificates thanks to OCSP, but can make a specific request for the certificate in question to the online responder. For a more detailed description, see the article "Basics Online Responder (Online Certificate Status Protocol, OCSP)„.
Event Sources
The events of the online responder are written to the application log. The following sources contain OCSP events:
- OnlineResponder
- OnlineResponderRevocationProvider (Microsoft-Windows-OnlineResponderRevocationProvider)
- OnlineResponderWebProxy
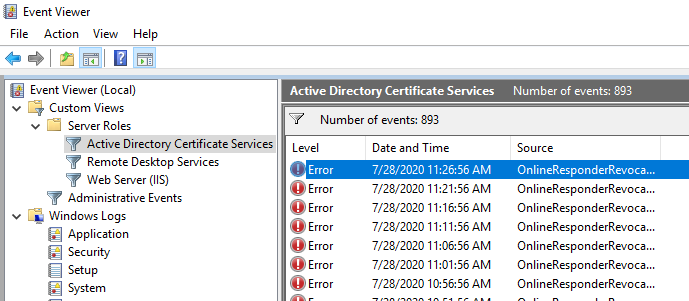
Predefined view in the Windows Event Viewer
An appropriately filtered view is preconfigured in the Active Directory Certificate Services category on each system where the online responder is installed.
Microsoft-Windows-OnlineResponder event source
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
| ID | Type | Event text |
|---|---|---|
| 17 | Information | Online Responder Service was started. |
| 18 | Information | Online Responder Service was stopped. |
| 20 | Error | The Online Responder Service did not start: %1. |
| 21 | Error | %1: The Online Responder Service detected an exception at address %2. Flags = %3. The exception is %4. |
| 22 | Error | OCSP Responder Services did not process an extremely long request from %1. This may indicate a denial-of-service attack. If the request was rejected in error, modify the MaxIncomingMessageSize property for the service. Unless exhaustive logging is enabled, this error will only be logged every 20 minutes. |
| 23 | Error | The Online Responder Service could not locate a signing certificate for configuration %1.(%2) |
| 24 | Information | The Online Responder Service successfully (re)loaded a signing certificate for configuration %1. |
| 25 | Warning | The signing certificate for Online Responder configuration %1 will expire soon. |
| 26 | Error | The signing certificate for Online Responder configuration %1 has expired. OCSP requests for this configuration will be rejected. |
| 27 | Warning | The signing certificate for Online Responder configuration %1 was not updated(%2). |
| 28 | Information | The signing certificate for Online Responder configuration %1 has been renewed. The hash for the new certificate can be located in additional data. |
| 29 | Error | Settings for Online Responder configuration %1 cannot be loaded. OCSP requests for this configuration will be rejected.(%2) |
| 31 | Warning | Performance counters for the Online Responder Service cannot be initialized. |
| 32 | Information | The Online Responder Service detected a change in the signing certificate template version for configuration %1. The old version was (%2,%3), the new version is (%4,%5). |
| 33 | Error | The Online Responder Service failed to create an enrollment request for the signing certificate template %2 for configuration %1.(%3). |
| 34 | Error | The Online Responder Service encountered an error while submitting the enrollment request for configuration %1 to certification authority %2. The request ID is %3.(%4) |
| 35 | Error | The Online Responder Service failed to install the enrollment response for configuration %1 for the signing certificate template %2 . The request ID is %3.(%4) |
| 36 | Information | The Online Responder Service successfully enrolled for a new signing certificate for configuration %1. The new certificate's hash can be located in additional data. |
| 37 | Warning | The signing certificate for Online Responder configuration %1 does not include the mandatory OCSP No Revocation Checking extension. You must configure an OCSP Response Signing certificate template to include this extension in all OCSP Response Signing certificates. For more information, see Configure a CA to Support OCSP Responders in the Online Responder console Help. |
Microsoft-Windows-OnlineResponderRevocationProvider event source
| ID | Type | Event text |
|---|---|---|
| 16 | Warning | For configuration %1, Online Responder revocation provider failed to update the CRL Information: %2. |
| 17 | Error | For configuration %1, Online Responder revocation provider either has no CRL information or has stale CRL information. |
| 18 | Error | For configuration %1, Online Responder revocation provider found a delta CRL referring to a newer Base CRL. |
Microsoft-Windows-OnlineResponderWebProxy event source
| ID | Type | Event text |
|---|---|---|
| 17 | Error | The Online Responder web proxy failed to Initialize. %1 |
| 18 | Information | The Online Responder web proxy is successfully loaded. |
| 19 | Information | The Online Responder web proxy is unloaded. |
| 20 | Information | The Online Responder web proxy detected an invalid configuration for the %1 property. The value was changed from %2 to %3. |
| 21 | Error | The Online Responder web proxy did not process an extremely long request from %1. This may indicate a denial-of-service attack. If the request was rejected in error, modify the MaxIncomingMessageSize property for the service. This error will only be logged every 20 minutes. |
Related links:
- Overview of Windows events generated by the certification authority
- Overview of Windows events generated by the Network Device Enrollment Service (NDES).
- Overview of Windows events generated by the Certificate Enrollment Policy (CEP) service
- Overview of Windows events generated by the Certificate Enrollment Web Service (CES).
External sources
- Windows Event Log Messages (WELM) (GitHub)
Comments are closed.