Assume the following scenario:
- An NDES server is configured on the network.
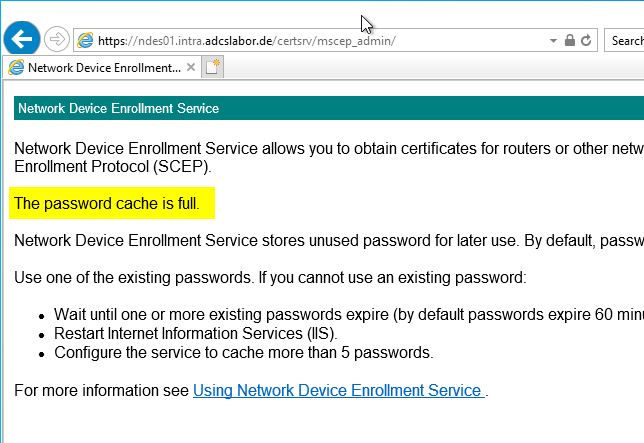
- When calling the administration web page (certsrv/mscep_admin) the following message appears:
The password cache is full.
The Network Device Enrollment Service (NDES) provides a way for devices that do not have an identifier in Active Directory (for example, network devices such as routers, switches, printers, thin clients, or smartphones and tablets) to request certificates from a certification authority. For a more detailed description, see the article "Network Device Enrollment Service (NDES) Basics„.
Cause
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
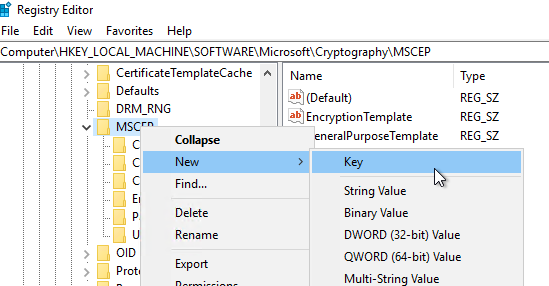
By default, five passwords can be in circulation within a one hour period. To increase the number of passwords in circulation, the "PasswordMax" value below the following registry key on the NDES server must be adjusted accordingly.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\MSCEP\PasswordMax
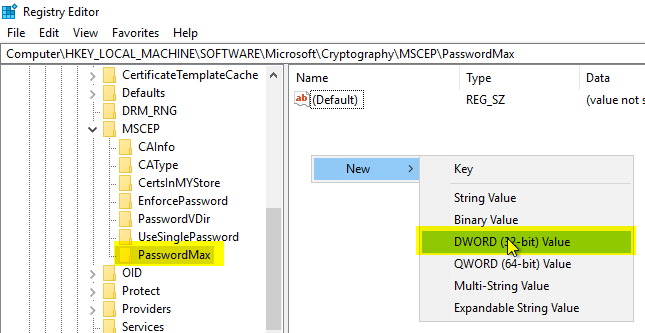
The above key is not present in the default setting and must be generated first.
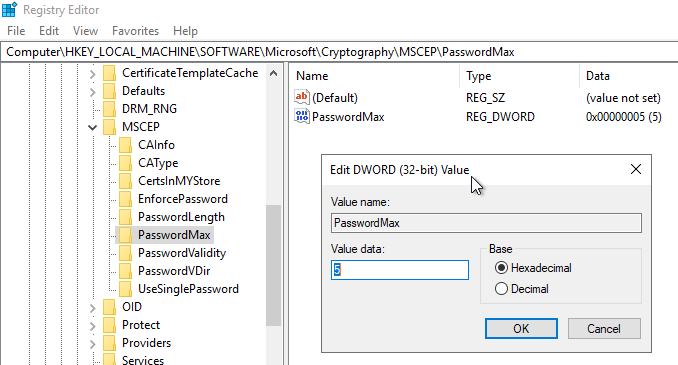
After that a new value called "PasswordMax" of type DWORD can be created. It is configured for the maximum number of passwords that may be in circulation at the same time.
The change requires a restart of the NDES service. For this, either the entire web server service can be restarted:
iisreset
Or you can restart the SCEP application pool on the IIS web server:
Restart-WebAppPool -Name SCEP
The NDES service is only loaded the first time it is called by a client. This can be forced with the following command:
[void](Invoke-WebRequest -Uri "http://localhost/certsrv/mscep/mscep.dll/pkiclient.exe?operation=GetCACaps")
Comments are closed.