Sometimes it is necessary to issue certificates with a shorter validity period than configured in the certificate template. Therefore, you may not want to reconfigure the certificate template right away or create another certificate template.
How is the expiration date of an issued certificate determined?
For the determination of the expiration date of a certificate, the Policy module of the certification authority. The expiration date of an issued certificate (NotAfter attribute) is determined based on the following conditions:
- The validity period defined in the associated certificate template.
- The maximum value configured on the respective certification authority (ValidityPeriod, ValidityPeriodUnits in the certification authority registry).
- The remaining validity period of the certification authority certificate.
The expiration date of the issued certificate is set to the shortest time in each case.
Can an applicant determine or shorten the expiration date?
It is possible to activate a fourth condition, which allows the requester to specify a desired end date or validity period via appropriate attributes when submitting the certificate request to the certification authority.
This method can only be used for Shorten of the certificate validity can be used. It is not possible to extend the intended certificate validity, in such a case the attributes are ignored by the certification authority.
In order for these attributes to be evaluated, the certification authority must first be configured to apply them. This is done via the flag EDITF_ATTRIBUTEENDDATEwhich must be configured in the policy module of the certification authority. By default, this flag is not enabled on Active Directory integrated certificate steles.
If the flag is not set, the attributes can be specified but are not processed by the certification authority. By default, the flag is not enabled on an Enterprise Certification Authority integrated into Active Directory.
Can I safely activate the flag?
Due to the previously described restrictions on processing the attributes, it is only possible to have the certificate issued in an even more restrictive manner. Therefore, it can be safely activated. Also for Microsoft Intune, setting this flag is official requirement.
How is the flag activated?
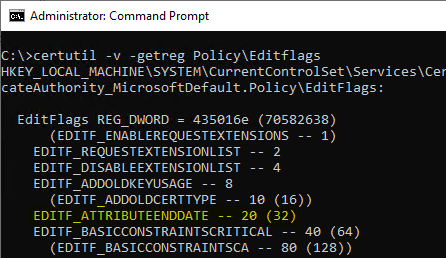
The current setting can be queried with the following command:
certutil -v -getreg Policy\Editflags
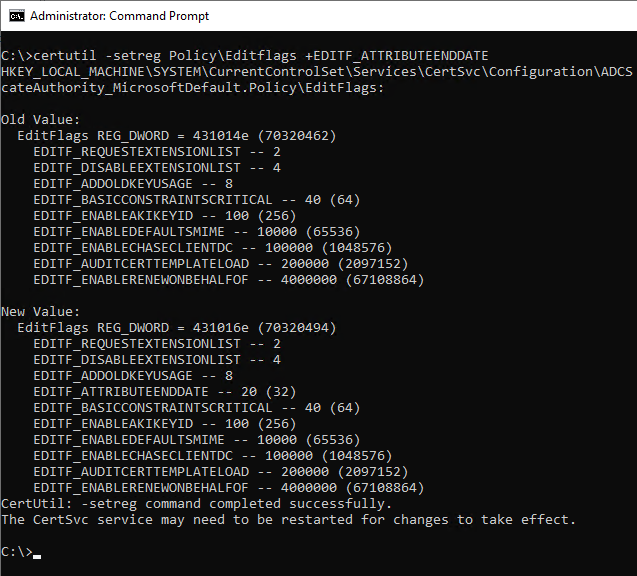
The flag can be activated with the following command:
certutil -setreg Policy\Editflags +EDITF_ATTRIBUTEENDDATE
The flag can be deactivated with the following command:
certutil -setreg Policy\Editflags -EDITF_ATTRIBUTEENDDATE
The certification authority service must then be restarted for the change to take effect.
Specifying the expiration date when submitting the certificate request
When submitting the certificate request, corresponding attributes can now be specified. Name and value are separated by colon. Several attributes in a row are separated by a line break ("\n").
| Value | Description |
|---|---|
| ExpirationDate | Date in as in RFC 2616 defined format. |
| ValidityPeriod | Minutes,Hours,Days,Weeks,Months,Years. Must be specified together with "ValidityPeriodUnits". |
| ValidityPeriodUnits | The number for the ValidityPeriod value. Must be specified together with "ValidityPeriod". |
The attributes can be specified when submitting via certreq.exe. Also a programmatic specification via the Submit Method of the ICertRequest Interface is possible.
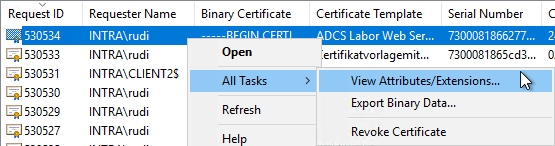
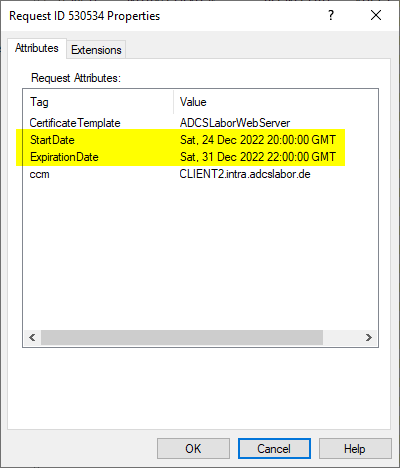
The information is transferred to the attribute table of the record in the certification authority database:
Examples
Since certificate requests usually do not contain any information about the certificate template to be used, this is specified in the same way in the example below with the "CertificateTemplate" attribute.
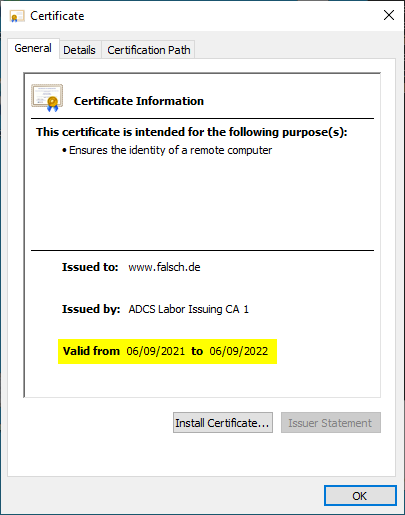
Issue a certificate valid for one year.
certreq ^ -config "ca02.intra.adcslabor.de\ADCS Labor Issuing CA 1" ^ -attrib "CertificateTemplate:ADCSLaborWebServer\nValidityPeriod:Years\nValidityPeriodUnits:1" ^ -submit "test.csr"
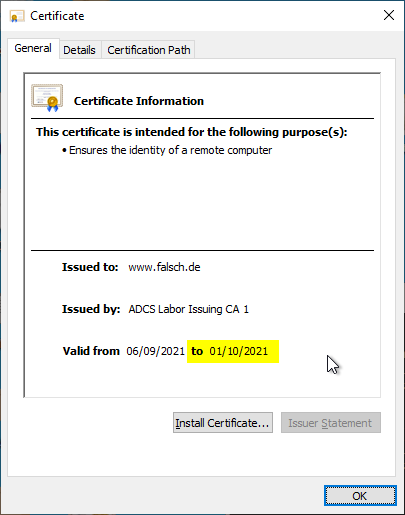
Issue a certificate which is due to expire on 01.10.2021.
certreq ^ -config "ca02.intra.adcslabor.de\ADCS Labor Issuing CA 1" ^ -attrib "CertificateTemplate:ADCSLaborWebServer\nExpirationDate:Fri, 1 Oct 2021 00:00:00 GMT" ^ -submit "test.csr"
Can an applicant request a different start date?
The Windows Defaul Policy module does not know an attribute to specify the start date (NotBefore attribute) of a certificate.
However, the function is not available since version 1.2 of the TameMyCerts Policy Modules via a "StartDate" attribute, which works analogously to the existing mechanism.
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
certreq ^
-config "ca02.intra.adcslabor.de\ADCS Labor Issuing CA 1" ^
-attrib "CertificateTemplate:ADCSLaborWebServer\nStartDate:Tue, 1 Mar 2022 00:00:00 GMT" ^
-submit "Typical_WebServer.req"
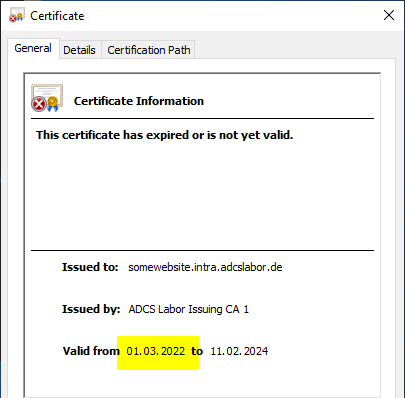
This makes it possible to set the validity period of a certificate to an exact period, for example for short-term access to IT resources.
Related links:
- Configuring a Secure Socket Layer (SSL) Certificate Template for Web Server
- Configuring a Certificate Template for Domain Controllers
- Configuring a Certificate Template for Remote Desktop (RDP) Certificates
External sources
- Change the expiration date of certificates that are issued by Certificate Authority (Microsoft)
- [MS-WCCE]: Windows Client Certificate Enrollment Protocol / szENROLLMENT_NAME_VALUE_PAIR (Microsoft)
- Microsoft Certificate Services - Format of ExpirationDate:Date attribute submitted in Certificate Requests (Microsoft TechNet Forums)
- RFC 2616: Hypertext Transfer Protocol - HTTP/1.1 - Date/Time Formats (Internet Engineering Task Force)
- Configure infrastructure to support SCEP with Intune (Microsoft)
Comments are closed.