There are situations in which you cannot operate NDES with changing passwords. This is usually the case when there is either no management solution for the devices to be managed, or when it cannot handle changing passwords.
In this case, you can configure NDES to generate a static password that will not change afterwards.
The Network Device Enrollment Service (NDES) provides a way for devices that do not have an identifier in Active Directory (for example, network devices such as routers, switches, printers, thin clients, or smartphones and tablets) to request certificates from a certification authority. For a more detailed description, see the article "Network Device Enrollment Service (NDES) Basics„.
This configuration is latently insecure, since anyone with knowledge of the password can arbitrarily request certificates for the certificate template stored in the NDES. If there are several applications in the network that require the use of a static password, it is advisable to provide a separate NDES server for each of them and - if feasible - to use a separate password for each application. renew the password at regular intervals.
Solution
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
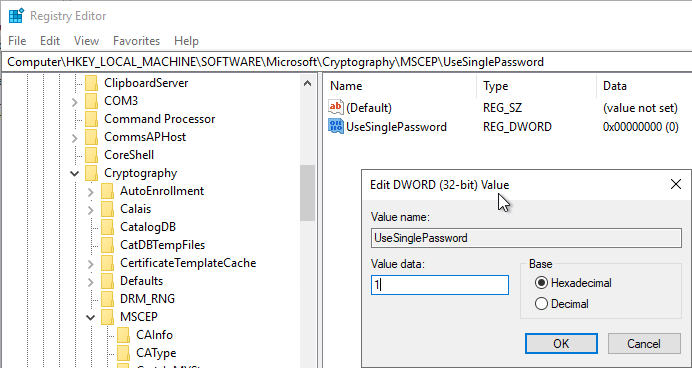
The desired setting can be found in the following registry key:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\MSCEP\UseSinglePassword
Below this is a 32-bit DWORD value called UseSinglePassword, which is set to 0 in the default installation. Setting the value to 1 enables the use of a static password.
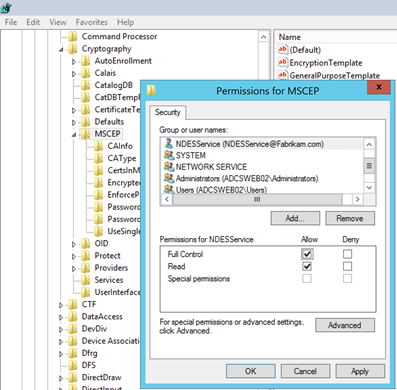
Since the static password is stored in the registry, the NDES service account must be granted write permission to the MSCEP registry key.
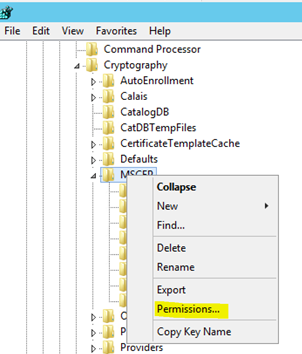
This is achieved via the "Full Control" authorization.
Provided that the NDES service runs with the identity of the IIS application pool, this can be entered with the following syntax:
IIS APPPOOL\SCEP
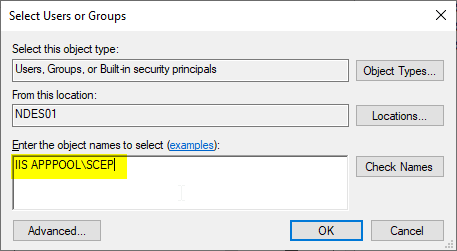
Please also limit the search range (Locations...) to the local machine.
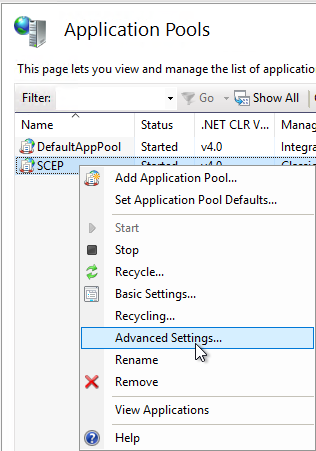
If the NDES service account is a domain account, the "Load User Profile" option must still be enabled in the advanced configuration of the IIS application pool.
Likewise, a user profile must exist, i.e. the NDES service account must log in to the NDES server interactively once for this to be generated.
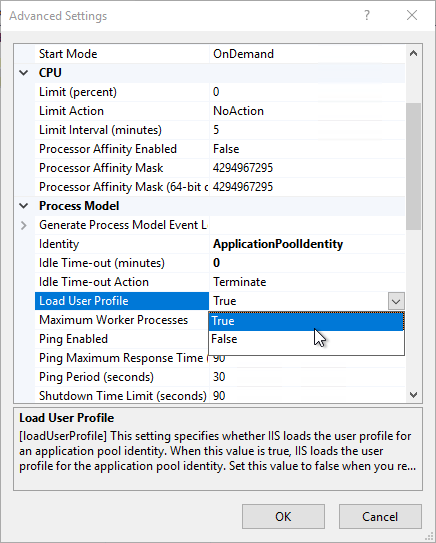
This setting can also be set with the following Windows PowerShell command:
Import-Module -Name WebAdministration
Set-ItemProperty IIS:\AppPools\SCEP -name processModel -value @{LoadUserProfile="true"}
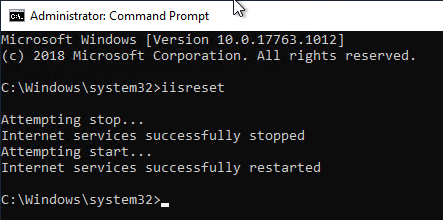
Afterwards, the NDES service can be restarted with the iisreset command so that the new configuration can be read in.
Each time the NDES server is started, it will display the Event no. 50 log to point out the configuration with the static password.
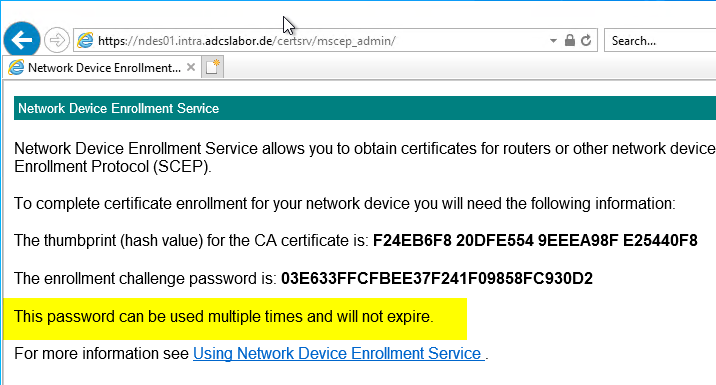
The NDES administration web page (mscep_admin) should now indicate that the password will not change.
Related links:
- Regular password change when configuring the Network Device Enrollment Service (NDES) with a static password.
- The Network Device Enrollment Service (NDES) logs the error message "The Network Device Enrollment Service cannot create or modify the registry key Software\Microsoft\Cryptography\MSCEP\EncryptedPassword."
- The Network Device Enrollment Service (NDES) logs the error message "The Network Device Enrollment Service cannot be started (0x80070002). The system cannot find the file specified."
- Installing the Network Device Enrollment Service (NDES) without Enterprise Administrator permissions
Comments are closed.