Sometimes it is necessary to verify a signature certificate of an online responder, for example when the connection to the (if present) Hardware Security Module (HSM) has to be verified. The online responder uses its own certificate store when the certificates are automatically retrieved from a certificate authority.
The Online Responder (Online Certificate Status Protocol, OCSP) is an alternative way of providing revocation status information for certificates. Entities that want to check the revocation status of a certificate do not have to download the complete list of all revoked certificates thanks to OCSP, but can make a specific request for the certificate in question to the online responder. For a more detailed description, see the article "Basics Online Responder (Online Certificate Status Protocol, OCSP)„.
Insight via the Microsoft Management Console
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
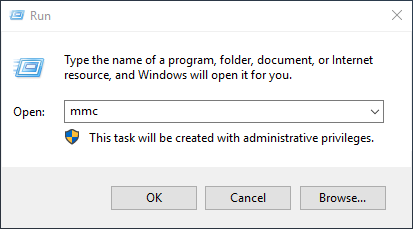
The certificate store can be viewed via Microsoft Management Console (MMC).
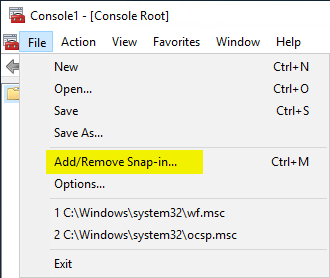
You add a new snap-in.
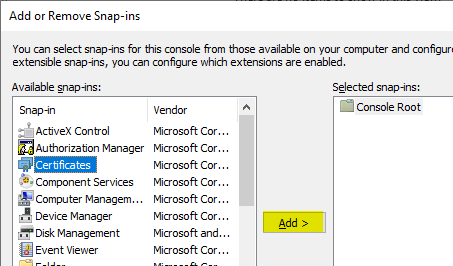
Select the Certificates snap-in and click Next.
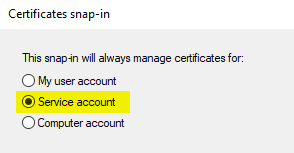
Then select that you want to view the certificate store of a service account and click Next.
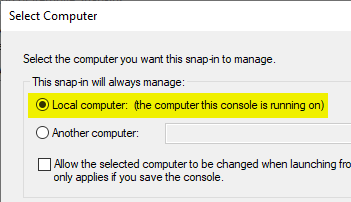
Select the local computer and click Next.
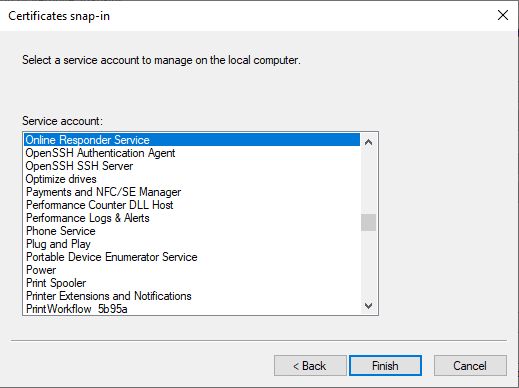
In the list of services, select the Online Responder Service and click Next.
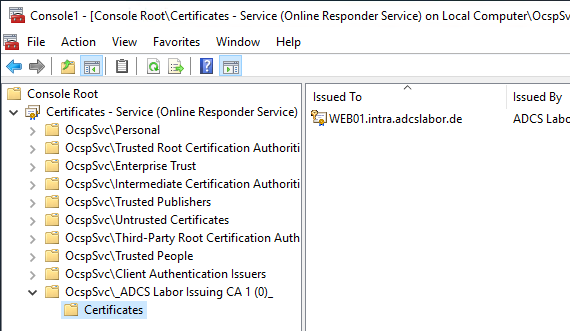
The signature certificates are located under OcspSvc\_{name of revocation configuration}_.
Insight via command line
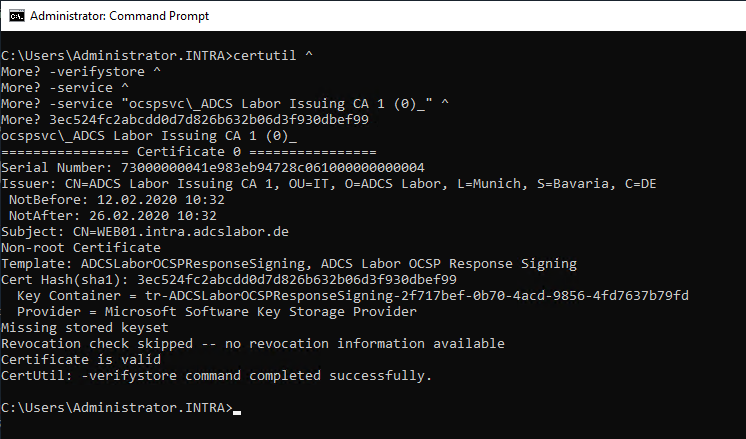
You can verify the signing certificate from the command line with the following command:
certutil ^
-verifystore ^
-service ^
-service " OcspSvc\_{Name der Sperrkonfiguration}_ " ^
{Thumbprint-des-Zertifikats}
Note that the -service argument must be listed twice.
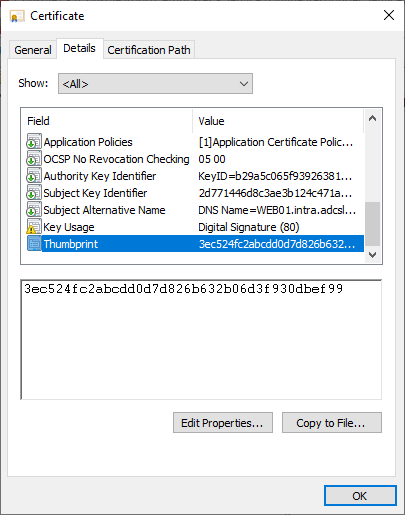
The thumbprint of the signing certificate can be identified from the previously opened management console. It is located in the Details tab of the respective certificate.